The rise of remote work necessitates effective mobile device management strategies. Two primary options exist: BYOD (bring your own device) and CYOD (choose your own device). Understanding the cost implications and level of control associated with each approach will enable you to make an informed decision that aligns with your organization’s security posture and budgetary […]
Maximizing employee mobility with BYOD and CYOD programs
Strengthen your passwords with NIST guidelines
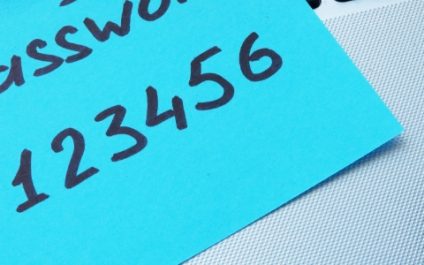
Many users unknowingly create weak passwords or mishandle them through common habits, leaving their data and accounts vulnerable to breaches. To combat this vulnerability, the National Institute of Standards and Technology (NIST) offers clear guidelines for crafting strong passwords and good practices to ensure password integrity. What is NIST? NIST is a US government agency […]
Mastering the art of cybersecurity: Training essentials for a resilient online presence

The significance of cybersecurity today cannot be understated. As technology continues to advance and businesses become increasingly reliant on digital systems, the risk of cyberattacks is at an all-time high. Small businesses are particularly vulnerable, as they may not have the resources or knowledge to implement robust cybersecurity measures. In this comprehensive guide, we will […]
Securing your cyber haven: A guide to understanding and preventing watering hole attacks

Watering hole attacks are a cybersecurity threat that can compromise the safety and integrity of your online activities. Let’s take a closer look at what they are, how they work, and what you need to do to protect yourself from falling victim to one. What is a watering hole attack? The term “watering hole” originates […]
The 2024 cybersecurity landscape: What to expect

The future is digital, and with it comes an ever-evolving cyber battlefield. Business owners, prepare yourselves, as 2024 promises a cybersecurity landscape unlike any before. Buckle up as we explore the five major trends defining the digital horizon — from the rise of AI-powered attacks to the blurring lines between the physical and virtual worlds. […]
Single sign-on: One password for multiple accounts

Say goodbye to password hassles and security worries! Single sign-on (SSO) simplifies access for employees while safeguarding company data. It’s the win-win solution for user experience and robust protection. What is SSO? In essence, single sign-on is a digital master key. It allows you to log in to multiple applications and websites using a single […]
Hack-proof your holidays: Essential tips for a cybersafe season

The holiday season’s flurry of activity can easily lead to a lapse in attention to work-related matters. Hackers may actively exploit moments when you’re deeply engrossed in holiday preparations, seeking out vulnerabilities in your systems. To prevent from being an easy mark this holiday season, incorporate these essential tips into your cybersecurity routine. Use strong, […]
Google Meet or Microsoft Teams: Who wins the video conferencing battle?

As the world shifts toward a more virtual environment, video conferencing tools like Google Meet and Microsoft Teams have become integral components of our daily communication. But the question remains: Which video conferencing app is better? Pricing For those on a tight budget, Google Meet and Microsoft Teams both offer a free version with limited […]
Stepping up your business security: The power of two-factor authentication and two-step verification

Every corner of the digital landscape hides potential threats to businesses. Luckily, you can fight back with a range of cybersecurity tools and technologies. Two of these resilient tools, two-factor authentication (2FA) and two-step verification (2SV), have become essential measures for any organization looking to protect its systems and data. 2FA and 2SV are often […]
Key considerations for picking a VPN solution

By using a virtual private network (VPN), you can prevent internet service providers from monitoring your online activities, access websites that are normally blocked with your current IP address, and ensure your privacy remains intact. But different VPN solutions offer different features, and it’s important for you to understand these before making a decision. Here […]

